Do you want to secure your WordPress site from hackers?
WordPress security isn’t just an option. Protecting your site from security risks like malicious code, malware, bots, and much more is necessary.
Every week Google blacklists over 10,000+ websites daily for malware and upwards of 50,000 for phishing. So if you’re serious about keeping your site safe, you’re in the right place.
In this WordPress security guide, we’ll show you how to secure your WordPress website from most security issues.
Can WordPress Be Secure?
WordPress can be a secure content management system (CMS) if you take the necessary site security measures. Below we’ll share the most essential website security precautions to take and explain why doing so is vital for your business website.
- 1. Understand Why WordPress Security Is Important
- 2. Keep WordPress Core Files Up to Date
- 3. Delete Unused Themes and Plugins
- 4. Use Strong Passwords and Permissions
- 5. Choose a Secure WordPress Hosting Company
- 6. Install a WordPress Backup Solution
- 7. Choose the Best WordPress Security Plugin
- 8. Use a Web Application Firewall (WAF)
- 9. Switch from HTTP to SSL/HTTPS
- 10. Limit Login Attempts
- 11. Use Two-Factor Authentication
- 12. Hide Your WordPress Login Page
- 13. Change Your Default Admin Username
- 14. Grant Admin Access by IP
- 15. Disable XML-RPC in WordPress
- 16. Disable File Editing
- 17. Scan Your WordPress Site for Malware
WordPress Security Basics
Let’s start by understanding why keeping your WordPress site secure is essential for your success and how to implement some basic security measures.
First, you might ask yourself why is WordPress security important?
1. Understand Why WordPress Security Is Important
Imagine waking up one day and finding your WordPress website compromised. All that work building a professional business site, blog, or eCommerce website is shattered by pesky hackers.
Hackers can introduce security vulnerabilities that not only damage your business revenue and reputation. They may also steal personal information, such as passwords and credit card details, and install malicious software that sends malware to your users.
What’s worse is you may fall victim to paying ransomware to regain access to your website.
If your site is a business and you want to avoid that nightmare, you need to pay more attention to your WordPress security. That begins with the simple practice of keeping your core version of WordPress up-to-date.
2. Keep WordPress Core Files Up to Date
Since WordPress is open source, it’s regularly maintained and updated. Your default WordPress installation will automatically install minor updates, but you’ll need to update WordPress to the latest version for major releases manually.
Similarly, WordPress has thousands of plugins and themes. The developers of these third-party tools also release regular updates.
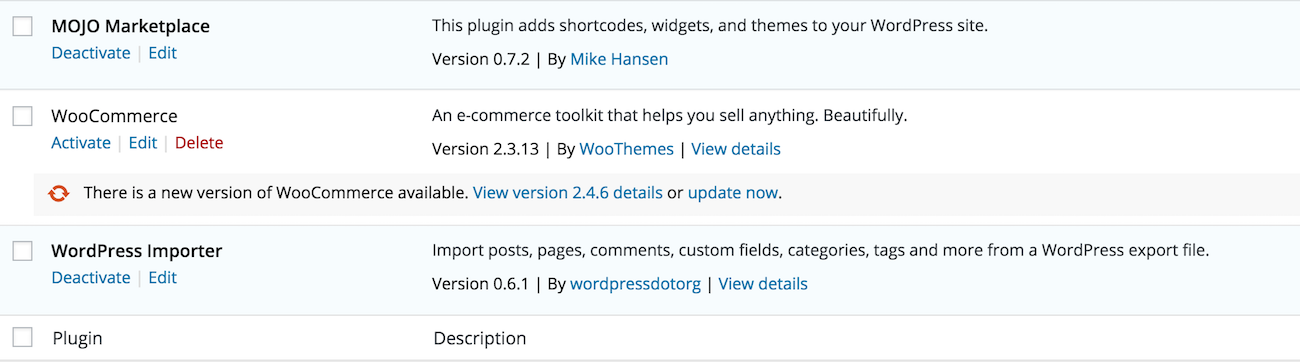
Plus, updates often contain security patches that fix vulnerabilities. So it’s vital to update your WordPress plugins and themes often to ensure your site’s stability and security.
3. Delete Unused Themes and Plugins
Besides keeping your plugins and themes updated, you should also delete any you no longer use.
Having unnecessary themes and plugins is like leaving your unused house doors unlocked. It offers a backdoor for hackers to gain access, so get rid of anything you don’t need.
4. Use Strong Passwords and Permissions
Some of the most common WordPress hacking attempts use stolen usernames and passwords to gain access to a website. To make hacking attempts more difficult, use strong passwords unique to your WordPress site.
This goes for your WordPress site, hosting, FTP accounts, business email address, and more.
While it’s tempting to use your pet’s name because it’s easy to remember, it’s also easy to guess.
The best practice is to use a password with at least 12 characters. Those characters should have upper and lowercase numbers, symbols, and letters.
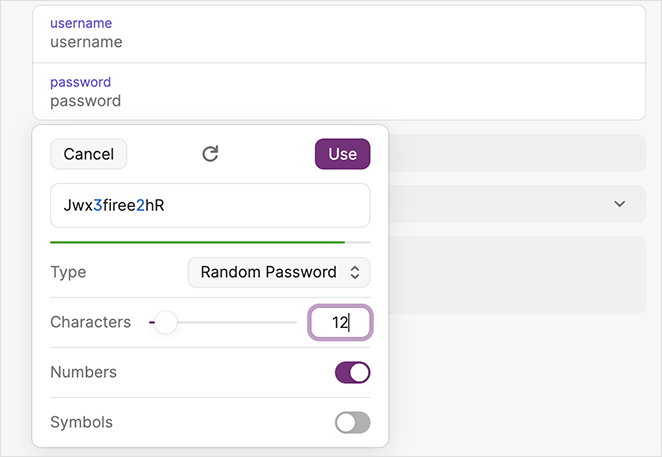
Many WordPress users avoid creating complex passwords because they’re hard to remember. The good news is you can use password managers to generate and store strong passwords securely.
Another important tip is to keep your WordPress admin account private. If you have a large team working on your site, or multiple WordPress authors, you can assign them specific user roles and permissions before adding their new user accounts.
5. Choose a Secure WordPress Hosting Company
Another basic security step is ensuring you use reputable web hosting. The best WordPress hosting providers, like Bluehost, SiteGround, and Hostinger, take extra care to protect their servers from security breaches.
A good WordPress hosting company will often work in the background to protect your site using the following measures:
- Monitor for suspicious activity
- Maintain tools to prevent large-scale DDOS attacks
- Keep server software, hardware, and PHP versions up-to-date
- Deploy disaster recovery and accident plans for major incidents
Many hosts offer shared hosting plans where you share web server resources with other customers.
Since this can risk hackers using neighboring sites to attack yours, it may be best to use managed WordPress hosting instead.
Managed WordPress hosting providers such as WPEngine have a more secure platform. They also offer automatic backups, WordPress updates, and advanced security.
No Code WordPress Security Steps
We understand that improving your WordPress security can be scary, especially for new website owners and beginners. Don’t worry; the steps below won’t require any technical expertise.
In a few minutes, you’ll be on your way to hardening your WordPress security without writing code.
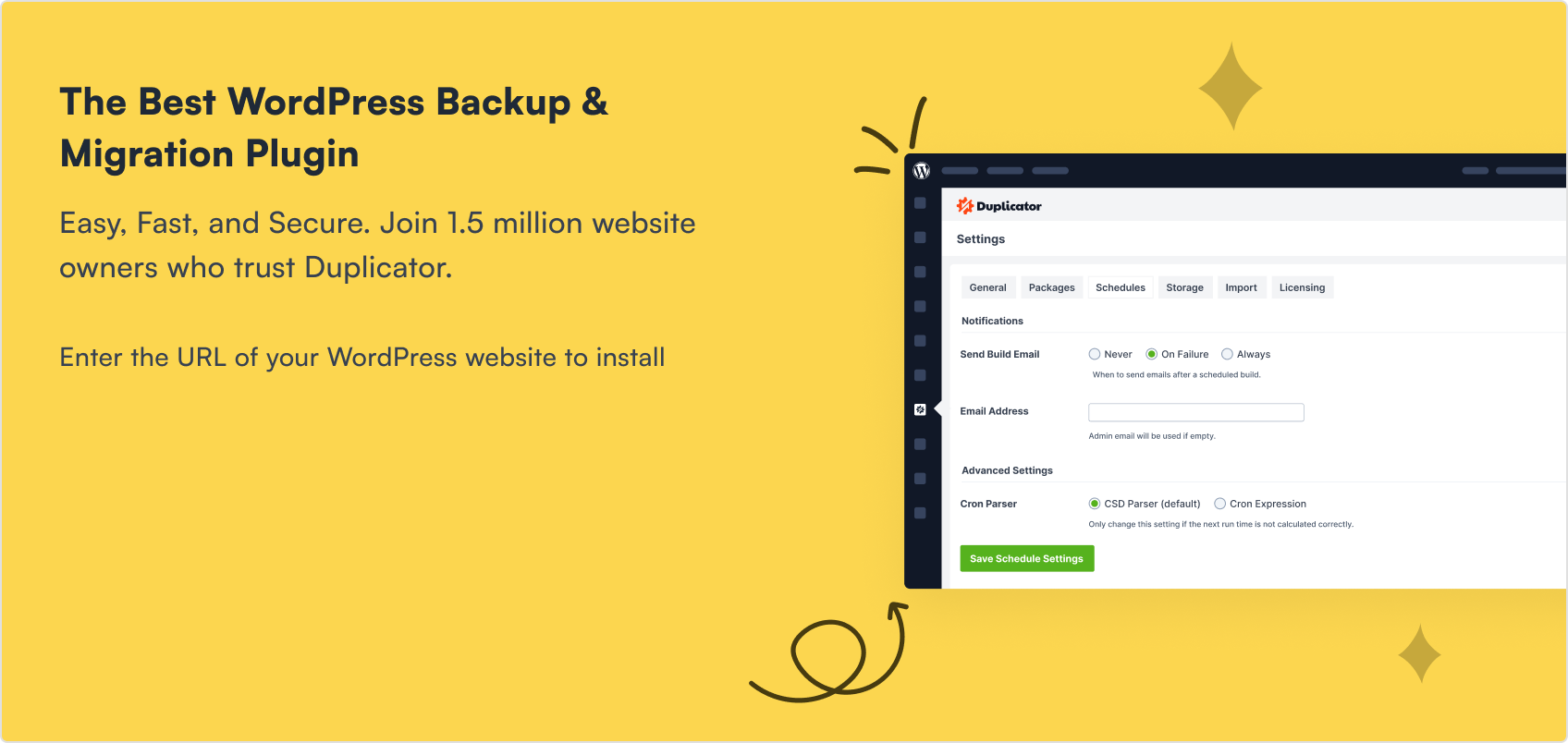
6. Install a WordPress Backup Solution
Backing up WordPress is one of your first defenses against hackers. If something terrible happens, they allow you to restore your site to the previous state.
The best WordPress backup plugins have free and paid versions with additional functionality, such as WordPress database and file transfers, recovery points, and email alerts. However, the most important feature to look for is the ability to regularly perform and save backups to a remote location.
Look for backup solutions with off-site storage on places like Amazon, Dropbox, or private cloud storage. Additionally, opt for plugins that allow backups to suit your schedule, such as once-per-day or real-time backups.
Some popular backup plugins with these features include Duplicator, UpdraftPlus, BlogVault, and Jetpack VaultPress Backups. They’re easy to use, reliable, and won’t require coding.
7. Choose the Best WordPress Security Plugin
After sourcing a backup solution, the next task is setting up a monitoring system to track the activity on your website. This activity can include failed login attempts, file integrity monitoring, malware scanning, and more.

Most of these monitoring tasks are easily handled by Sucuri Scanner, the best free WordPress security plugin. After installing and activating Sucuri, navigate to Sucuri Security » Settings from your WordPress dashboard and click the Hardening tab.
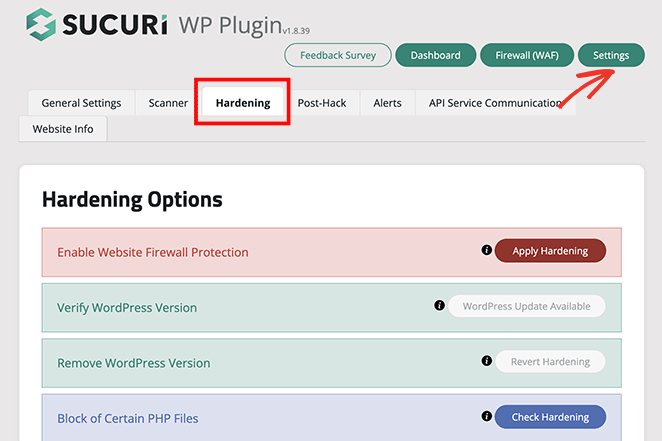
Now go through each option and click the Apply Hardening button.
These settings help lock down areas of your site that hackers often use in their attacks. The only option you’ll need to pay to upgrade is the Web Application Firewall which we’ll explain in the next step.
Other alternative WordPress security plugins include WordFence and iThemes Security.
8. Use a Web Application Firewall (WAF)
Using a firewall is an effective way to block malicious traffic before it reaches your WordPress site, and there are several types to choose from.
- DNS Level Website Firewall: Routes site traffic through cloud proxy servers, sending only genuine traffic to your web server.
- Application Level Firewall: Examines traffic once it reaches your server but before loading WordPress scripts.
As mentioned above, Sucuri’s firewall is a robust solution for this. Sucuri helped WPBeginner block 450,000 attacks in 3 months, proving its effectiveness.
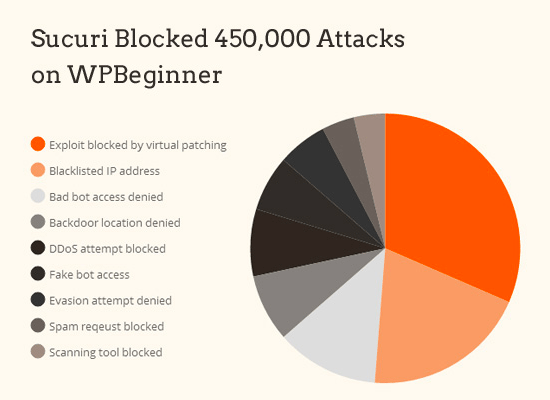
The plugin also comes with malware cleanup and a blacklist removal guarantee, so if you’re hacked while using them, they’ll fix your site, no questions asked. Considering most security experts charge around $250 per hour, this service is a steal at only $199 per year.
Enhance your WordPress security with Sucuri Firewall today.
9. Switch from HTTP to SSL/HTTPS
If you haven’t already, adding SSL encryption to your WordPress site is a crucial next step. SSL, short for Secure Sockets Layer, encrypts data transfers between your site and visitor’s browsers. It basically makes it harder for hackers to steal information.
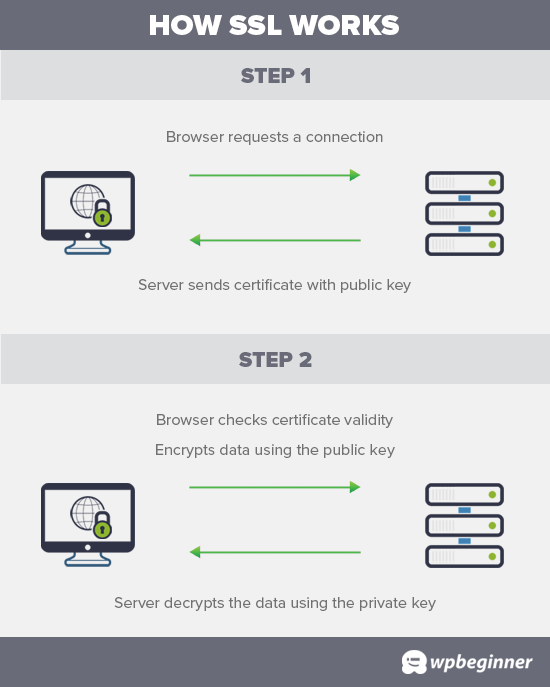
Once SSL is enabled, your site will use HTTPS instead of HTTP. There will also be a padlock icon next to your address in web browsers.
SSL certificate prices range from 80 to hundreds of dollars annually, making it something many site owners avoid. However, since Let’s Encrypt began offering free SSL certificates, many hosting companies offer them as part of their plans.
If your web host doesn’t offer SSL, you can buy one from domain.com. They have the most reliable SSL deal, with a $10,000 security warranty and TrustLogo security seal.
Advanced WordPress Security Tips
Once you’ve mastered the security steps above, it’s time to level up. There’s always more you can do to secure your WordPress site, let’s explore some advanced security measures.
Note: Some of the steps below may require coding knowledge.
10. Limit Login Attempts
To further protect your site against the threat of brute force attacks, you can limit attempts to log into WordPress. That way, when someone enters the wrong password repeatedly, they’re locked out of your site for a time.
One way to implement this feature is to use the Limit Login Attempts Reloaded plugin.
It lets you specify the maximum number of incorrect passwords allowed before locking out the user and emails you whenever a login fails.
For full instructions on setting up this plugin, check out this guide on how to limit login attempts in WordPress.
11. Use Two-Factor Authentication
Two-factor authentication makes the login process for legitimate users more complicated and annoying and helps keep undesirables from your website.
As the name implies, two-factor authentication requires users to complete two security steps before they can use the site. The first step is usually the traditional name/password challenge. The second step involves entering a security code sent to them via text message or other secure device.
Plenty of plugins allow you to set up two-factor authentication, such as the free WordPress Two Factor Authentication plugin.
After installing and activating the plugin, click the Two Factor Auth link in your WordPress admin, which reveals a one-time setup code.
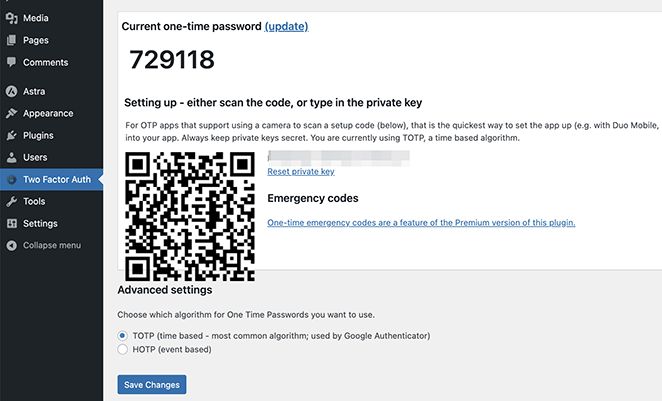
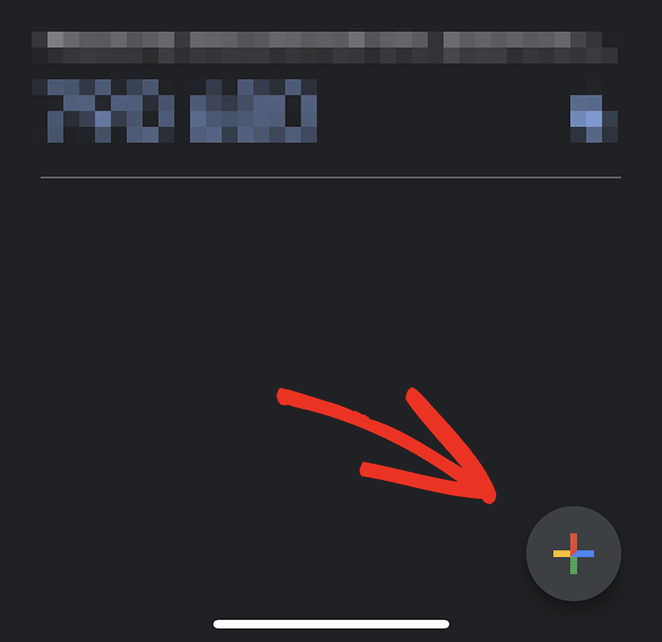
Next, install and open an authenticator app on your phone, such as Google Authenticator, and click the plus icon to add a new code.
From there, you can scan the QR code on the plugin’s setting page to finish the setup.
The next time you log into your WordPress site, it will ask you for the two-factor auth code after entering your password.
12. Hide Your WordPress Login Page
Almost all hackers know that a WordPress admin page is typically accessed by adding /wp-admin after the domain name. For example, if your domain name is xyz.com, your admin page is probably accessed by the following URL: http://xyz.com/wp-admin.
They also know that the name of the login page is wp-login.php.

Fortunately, you can change that. Plugins, such as WPS Hide Login, allow you to customize your login URL.
It becomes much more difficult for hackers to break into your system if they can’t find your login page. You can also follow this guide on how to change your WordPress login URL.
13. Change Your Default Admin Username
Similarly, your WordPress installation may give administrator accounts the username “admin.” It’s best to change this name as soon as possible because hackers are familiar with it and may try a “brute force” hack (attempting various passwords repeatedly) with that username.
Many host providers are aware of this potential for an attack and, as a result, avoid creating the administrator account with the name “admin.” However, it’s still worth checking to enhance your security.
14. Grant Admin Access by IP
If you’re the only one authorized to perform administrative tasks on your WordPress site, you can also restrict administrative access by IP address.
Your IP address is a quartet of numbers that identifies you online. Think of it as your digital address.
With this in mind, you can tell WordPress only to allow people to access the admin if they have a specific IP address. That means hackers trying to access your site from any other IP will be unsuccessful.
To implement this security feature, go to whatismyip.com to discover your IP address. Then, you’ll need to modify your .htaccess file on your host provider’s admin directory to make the security change.
If you don’t know how to do that, call your hosting company’s tech support line and ask a technician to do it for you.
Specifically, you’ll want something that looks like this added to the file:
<Files wp-login.php>
order deny,allow
Deny from all
Allow from xxx.xxx.xxx.xxx
</Files>
Replace the “xxx.xxx.xxx.xxx” with the IP address you saw on whatismyip.com. Once that’s done and the file is saved, only people with that specific IP can access your WordPress admin.
Note: Your Internet Service Provider (ISP) will sometimes change your IP address. If that happens, you’ll be locked out of your site. The solution is to call tech support and ask a technician to update the IP address accordingly. Do this at your own risk.
15. Disable XML-RPC in WordPress
ML-RPC is a feature introduced in WordPress 3.5 that helps connect your WordPress site with web and mobile apps. However, due to how powerful it is, it can also amplify brute-force attacks.
For example, previously, if a hacker wanted to try 500 different passwords, they’d have to make 500 login attempts which the limit login attempt plugins would typically catch. However, with XML-RPC, hackers can use the system.multicall function to try thousands of passwords with fewer requests.
Consequently, if you’re not using XML-RPC, it’s best to disable it. For full instructions, see this guide on how to disable XML-RPC in WordPress.
16. Disable File Editing
WordPress has a built-in code editor that lets you edit WordPress theme and plugin files from your WordPress admin area. In the wrong hands, this feature can risk the security of your site, which is why it’s best to turn it off.
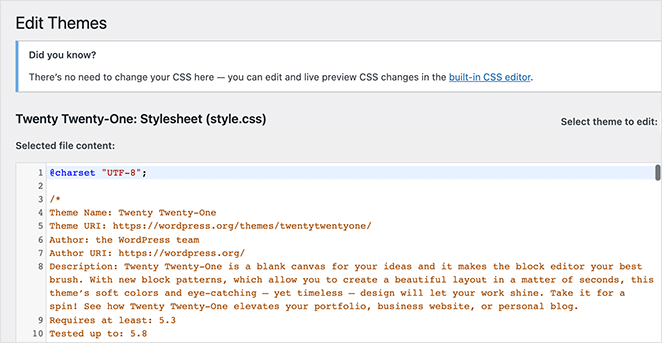
You can do this easily by adding the following code to your wp-config.php file.
<Files *.php>
deny from all
</Files>
Alternatively, you can turn off file editing using the Hardening feature in the free Sucuri plugin mentioned earlier.
17. Scan Your WordPress Site for Malware
You probably already have anti-virus software on your PC that scans your hard drive for potential threats. If you have a WordPress security plugin installed, it will routinely check your site for security breaches and malware.
However, a sudden drop in your website traffic or search engine rankings could indicate something’s wrong, and you should run a manual scan. You can use your WordPress security plugin or malware and security scanner for this.
Running an online scanner is straightforward. Simply enter your website URLs, and the scanner will crawl your site looking for malware and malicious code.
While these scanners can scan your website, they can’t remove the malware or clean a hacked site.
Next Steps
We hope you found this guide on how to secure your WordPress site from hackers helpful. Your WordPress site is just as susceptible to intrusion as any other site on the web, but you can mitigate the risk of an attack by following the best WordPress security practices.
For further reading, check out the following tutorials and guides:
- Best WordPress multisite plugins
- How to password protect a WordPress site
- Best WordPress duplicator plugins
- How to accept secure Stripe payments in WordPress
Thanks for reading! We’d love to hear your thoughts, so please feel free to leave a comment with any questions and feedback.
You can also follow us on YouTube, X (formerly Twitter), and Facebook for more helpful content to grow your business.





Hello, friend my question is that, please tell how to secure wordpress blog /site from hackers? Is this responsibility of hosting providers or my-self. Kindly tell some plugins for wordpress.,.
The best way to secure your WordPress website is not by using a plugin but by denying access to certain directories through htaccess file and your robots.txt file. Also choose a secure hosting provider.
The tips that you added are so helpful. But for securing WordPress, you need to give more emphasis to the security of your login area. You need to pay more attention on strengthening your admin login area.
Nice Article!
Security of the website is the key.
1. Choose a best hosting provider.
2.Your WordPress website must have a strong user name & password, keep Admin Dashboard secured.
3.Only used best rated plugins.
4.Monitor your website time-to-time. Take Regular site backups and cleanup unused plugins.
5. Update your site’s WordPress Versions.
I was wondering if you ever thought of changing the page layout of your blog?
Spot on regarding why more WP users should secure their sites and go beyond security plugins, even though many are excellent. Website hacking is becoming more of a sport it seems, so protecting our sites and customer data is fundamental.
Using a VPN service and proxy server can also helps in securing your wordpress site or blog from getting hacked.
What a relevant information you have shared. I follow the same procedure to keep my website safe. I also use Ace Vpn to keep my data safe and secure while surfing especially paying someone online.